Introduction
In today’s interconnected digital world, securing online transactions has never been more critical. Unfortunately, traditional username-password systems often fail to provide the necessary protection, making them an Achilles heel in cybersecurity strategies. A significant step forward in the security domain comes from FIDO’s WebAuthn protocol, which is now included in Cloudentity as an authentication mechanism in Cloudentity. This protocol not only boosts security but also promises to replace insecure password logins altogether.
Problems with Passwords
In the digital landscape, passwords, once online security’s mainstay, have become a profound liability. The inherent weaknesses of passwords expose users to numerous threats, escalating the risk of breaches and fraudulent activities. The list of security concerns includes:
-
Brute Force Attacks: Cybercriminals systematically try all possible password combinations until the correct one is found.
-
Leaked Passwords: A single data breach can expose passwords, putting multiple accounts at risk due to the common habit of password reuse.
-
Credential Stuffing: Attackers exploit leaked usernames and passwords, attempting mass logins across various platforms and making every reused password a potential gateway to unauthorized access.
-
Phishing Attacks: Deceptive tactics can trick unsuspecting users into divulging their passwords, compromising even the most complex ones. Similarly, keyloggers can track user keystrokes to identify passwords employed by a user.
-
Password Sharing: The widespread practice of sharing passwords, often for convenience, further intensifies potential security risks.
Alongside these security issues, passwords also pose significant user-experience challenges that complicate the online journey:
-
Complexity Requirements: Users often encounter stringent password policies during registration, requiring a mixture of letters, numbers, and special characters. These complexity requirements, while intended for increased security, often lead to convoluted passwords that are hard to remember but surprisingly easy for machines to guess. This also stalls the user’s registration flow in a significant way.
-
Remembering Passwords: With an ever-growing list of online accounts, remembering passwords becomes a daunting task. The ‘password fatigue’ that results can lead users to resort to insecure practices like password reuse or simple, easily remembered (and guessed) passwords.
Benefits of WebAuthn
WebAuthn (Web Authentication) is an open standard for web-based public key cryptography. This state-of-the-art technology allows users to authenticate to online services using biometrics, mobile devices, or FIDO security keys, greatly reducing the risk of password-based logins.
WebAuthn’s main strength lies in its support for password-less logins, thereby eradicating the security vulnerabilities and user-experience issues associated with password use.
Note
Athough they describe different technical processes, for the purposes of this document “passkeys” and “WebAuthn” are used interchangeably. The WebAuthn standard paves the way for passkeys to be used as an authentication mechanism for many web applications, but the net benefit is still the elimination of passwords.
Let’s delve into how WebAuthn is revolutionizing online security:
Elevated Security
WebAuthn stands as a groundbreaking solution to the perennial problem of password security; it eliminates the need for passwords, rendering such attacks futile. Here is how this protocol addresses each of the challenges associated with traditional password use:
-
Brute Force Attacks: WebAuthn utilizes public-key cryptography instead of passwords. During the registration process, a unique key pair (consisting of a private and a public key) is created. The private key is securely stored on the user’s device and is never shared or transmitted. As a result, there is no password that could be cracked via brute force methods.
-
Leaked Passwords and Credential Stuffing: With WebAuthn, the absence of a stored password eliminates the risk of password leaks. Furthermore, the protocol’s reliance on the unique private key stored on the user’s device renders credential stuffing attacks ineffective. Even if a user’s identifier is leaked, without the corresponding private key (which only the genuine user’s device has), an attacker cannot gain access.
-
Phishing Attacks: In the WebAuthn protocol, the authentication process involves a challenge-response mechanism. The server sends a unique challenge to the client, and the client responds with a signature created using the stored private key. The server verifies this response with the stored public key. This interaction negates the risk of phishing as there are no passwords to be “fished” by attackers.
-
Password Sharing: The user’s authentication in WebAuthn is device-bound and optionally supplemented by a biometric or a PIN, thus eliminating the need (and even the possibility) for password sharing.
Reinvented User Experience: No Forgotten Passwords and OTPs
Indeed, WebAuthn is not just a robust security protocol; it is also designed to significantly enhance the user experience. Here’s how it effectively addresses and improves upon several common user-experience challenges associated with traditional password usage:
-
Simplifying Complexity Requirements: With WebAuthn, the need for users to generate and remember complex passwords is entirely eliminated. The protocol leverages public-key cryptography for authentication, rendering the creation of complicated, hard-to-guess passwords unnecessary.
-
Eliminating the Need to Remember Passwords: WebAuthn eliminates the most dreaded aspect of password-based systems - the need to remember multiple complex passwords. Users can authenticate themselves using hardware tokens, mobile devices, or biometric authentication like fingerprint or facial recognition. These methods, far more intuitive than memorizing strings of characters, provide a more seamless user experience.
-
No More One-Time Passwords (OTPs): One-time passwords, although an added layer of security, can be a hassle for users. OTPs often require users to switch between applications or devices to complete the authentication process. With WebAuthn, OTPs are no longer necessary as it provides a higher level of security without the added inconvenience.
-
Supports Various Login Methods: WebAuthn can be used with a broad range of authenticators, which are usually used to unlock the trusted vault where keys are stored (as in the case of passkeys). This flexibility enables users to choose their preferred login method based on convenience and security requirements, such as using a fingerprint scanner on a laptop or a security key on a desktop.
-
Streamlined Registration and Login Process: Beyond the absence of passwords, WebAuthn significantly simplifies and streamlines the registration and login processes. The protocol’s design allows for quick and easy setup of security keys or biometrics during registration, and a one-touch or one-glance login experience. This ease of use not only reduces the time spent on these processes but also enhances overall user engagement and satisfaction.
Future-Proofing Organization’s User Management and Storage
In today’s fast-paced digital age, businesses must always be prepared to adapt and evolve. The adoption of Cloudentity’s implementation of WebAuthn positions your business at the forefront of this evolution, equipping it to thrive in an impending password-less future.
Many major technology giants have already begun moving towards password-less systems, recognizing the benefits of increased security and improved user experience. For instance, Apple’s Face ID and Touch ID provide secure, password-less access to devices and applications based on the WebAuthn standard. Google has had password-less authentication on its roadmap for many years.
The improved user experience offered by WebAuthn can lead to higher user retention. Users appreciate simplicity and convenience. By removing the hurdles associated with password use, businesses can foster a more seamless user experience, leading to increased customer satisfaction and loyalty.
In essence, moving to Cloudentity isn’t just about embracing a new technology. It’s about strategically positioning your business to thrive in the changing landscape of digital security and user experience, standing side by side with industry leaders, and cultivating enhanced customer loyalty.
Challenges with WebAuthn
While WebAuthn provides substantial benefits for improving online security and user experience, it’s important to acknowledge that this protocol also presents several challenges. Let’s discuss these in detail:
-
Cross-Ecosystem Portability: WebAuthn is designed to use local authenticators such as biometrics or security keys which are bound to a particular device. This poses a challenge when users need to access their accounts from different devices, as they may not be able to carry their authenticators with them.
Some ecosystems, like Apple’s Keychain, store credentials in a vault that is shared between devices, like a user’s iPhone, iPad and Mac laptop. However, when a user needs to change to a different ecosystem, like a Windows or Android platform, the credentials in the Keychain vault will not be available. This is particularly problematic for users who frequently switch between devices or platforms.
-
Limited Browser Compatibility: Although support for WebAuthn is increasing, not all browsers and platforms are fully compatible with this protocol as of now. Some users may find themselves unable to take advantage of WebAuthn’s benefits due to their choice of browser or operating system.
-
Passwords as a Second Authentication Factor: While WebAuthn promotes password-less authentication, there are scenarios where passwords might still be used as a secondary authentication factor. This not only negates the user experience benefits but also exposes the system to the same security vulnerabilities associated with password use.
-
Inability to Share Passkeys Remotely: Unlike passwords, biometrics and security keys can’t be easily shared remotely. This poses challenges for certain use-cases that require account sharing, like family accounts for digital services, or for providing temporary access to a service. However, legitimate credential-sharing cases are considered to be very limited.
Each of these challenges presents an area for further exploration and development as the digital world continues to move towards adopting password-less authentication systems. As with any technological evolution, it’s essential to balance the rewards with potential risks, continually refining the solution until it becomes a seamless part of our digital lives.
Conclusion
The deployment of WebAuthn within Cloudentity heralds a significant advancement in cybersecurity. It offers a solid and secure alternative to conventional password logins, providing a superior line of defense against cyber threats as well as a more user-friendly experience.
As businesses adapt to this innovative solution, they’re not only bolstering their current security posture; they’re also getting ready to navigate the cybersecurity landscape of the future. The days of passwords may be numbered, but with platforms like Cloudentity implementing WebAuthn, we are well-equipped for a safer digital journey ahead.

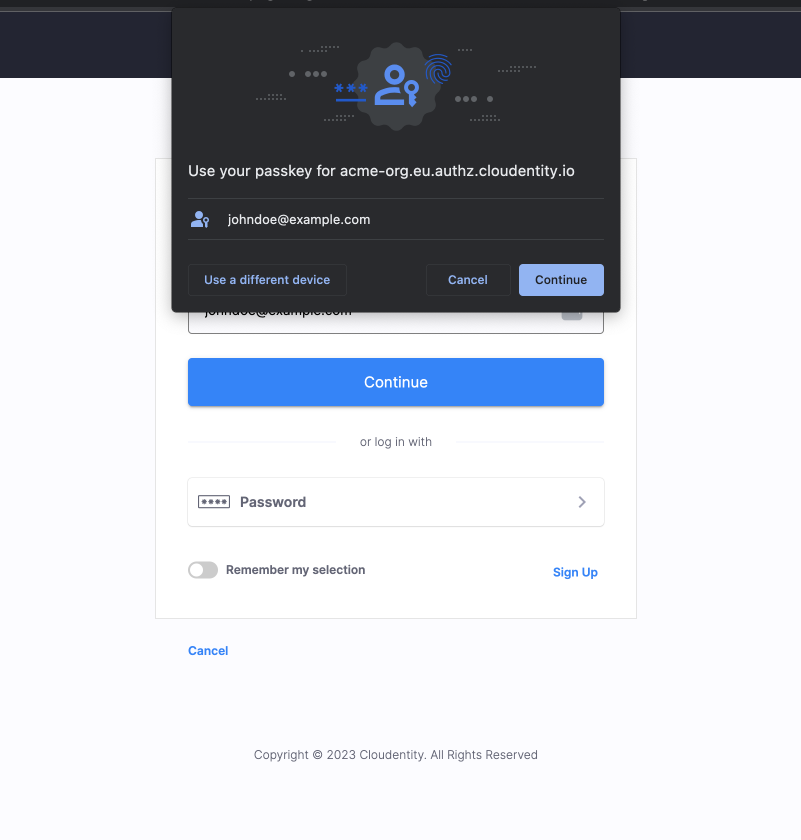
Cloudentity supports password-less authentication using WebAuthn.
Register for free to get access to a Cloudentity tenant and we’ll get you started on your password-elimination journey!
